Threat and Risk
Assessment Services
Understand the level of risk your assets are facing
What is a Threat and Risk Assessment?
A Threat and Risk Assessment (TRA) determines the threat sensitivity of your digital assets, the controls in place, residual vulnerabilities, and the various threats to your environment.
It helps you determine the level of risk faced by your assets, and it will recommend the appropriate level of protection to mitigate those risks.

When Should You Perform a TRA?
It’s best practice to conduct a TRA if you are adding new assets, applications or systems to your environment, making modifications to your existing environment, or sharing information with third-party entities. A TRA can help you prevent exposing your business to undue cyber risk that can affect your reputation and bottom line.
Protect Your Data and Enhance Security Program ROI
Improve the effectiveness of your controls
Understand the effectiveness of existing and proposed controls. Know the residual vulnerabilities of your assets, and leverage our recommendations to lower risk of threats.
Demonstrate cyber competency
Provide visibility of your organization’s cybersecurity posture to senior management, your board, external stakeholders, regulators, and clients. Your TRA details will be documented in a structured data-risk repository.
Plan for the future
Enhance your ROI of the security programs you have in place by assessing their effectiveness through our TRA service. The recommendations can be leveraged to prioritize future actions and improve your risk management programs and cybersecurity posture.
Our Approach to Threat and Risk Assessments
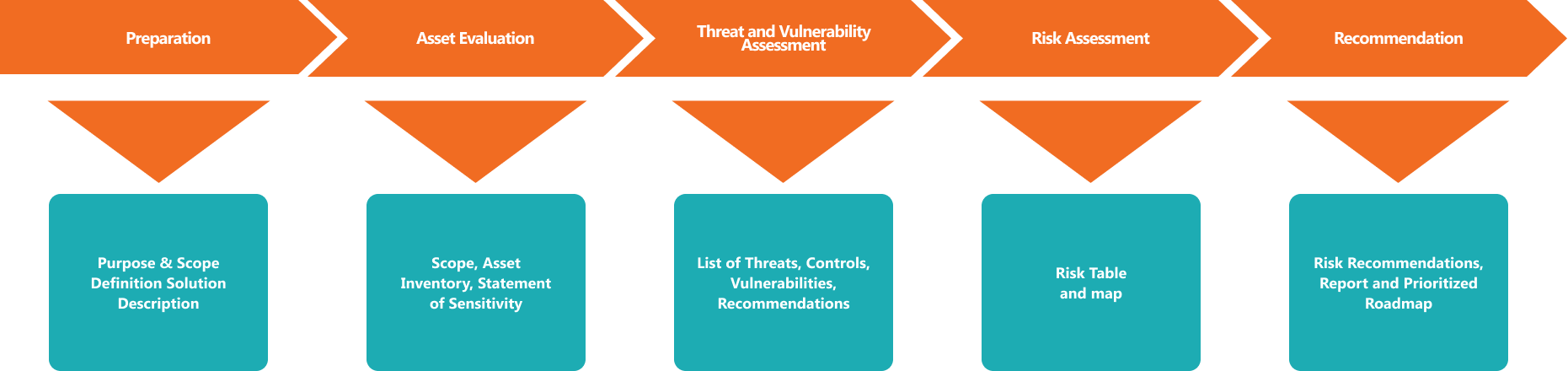
Preparation
Asset Evaluation
Threat and Vulnerability Assessment
Risk Assessment
Recommendation
• Purpose and Scope Definition
• Solution Description
• Scope
• Asset Inventory
• Statement of Sensitivity
• List of Threats and
Vulnerabilities
• List of Controls
• Recommendations
• Risk Table and Map
• Risk Recommendations, Report
• Prioritized Roadmap
Integrated Risk Assessment Process
The ISA Cybersecurity Difference
Over 30 years of experience delivering cybersecurity services.
Get recommendations that keep your data safe, reduce costs, improve key metrics, and protect your brand reputation 24/7/365.
We work on your terms and tailor our services to meet your needs.
Our success is measured by the degree to which our customers stay cyber secure.
In Need of a Virtual CISO or Senior Cyber Talent?
Our innovative Role-based Consulting services provide skilled talent needed to bridge a team gap quickly and reliably. From managing business changes, evaluating new technology, or simply keeping the lights on – we can help.



