Follow ISA Cybersecurity on LinkedIn for the latest cybersecurity news
Weekly CyberTip: Consider supply chain in your incident response plan
You may feel you’re ready to face an in-house cyber incident. But are you ready to respond in the event that part of your supply chain is affected? Here are some tips to consider when reflecting on your incident response planning:
• catalog partners and suppliers and conduct a supply chain vulnerability audit
• establish secure communications protocols and incident notification processes
• consider reserve inventory requirements, explore alternative suppliers in advance
• implement security tools and strategic network configurations to limit exposure
• limit access and data exchange to minimum necessary for business purposes
• limit and audit access controls using a zero-trust model
• vet and regularly audit suppliers
• document and test your incident response plan with your partners
Healthcare organizations targeted by Evernote phishing scheme
An August 10 bulletin from the U.S. Department of Health and Human Services’ Health Sector Cybersecurity Coordination Centre warns healthcare organizations to be on the look-out for a widespread phishing campaign referencing Evernote software. “The campaign has a subject of “(Victim Organization) (Date) Business Review” and utlizes [sic] a Secure Message theme. Inside of the email is a malicious link which lures the recipient to a Victim Organization themed Evernote site,” explains the bulletin.
Once connected to the fake site – which is designed to look like an Evernote interface – a malware-infected HTML download is delivered to the victim. The malware is designed to harvest email credentials and other personal information.
Evernote is a popular note-taking and to-do list management application that enables easy sharing of information across multiple devices and platforms. That flexibility has made it popular in the healthcare sector, but introduces risk if a user falls prey to social engineering attack.
The bulletin includes a detailed list of indicators of compromise (IOCs) involved the phishing campaign, along with a number of preventative measures that should be taken to reduce the risk of compromise. Key among them is security awareness training for users to ensure that they are vigilant in watching for unsolicited or suspicious email messages.

Cisco confirms May data breach
On August 10, Cisco confirmed that they were the target of a successful cyber attack and data breach in May 2022. “The incident was contained to the corporate IT environment and Cisco did not identify any impact to any Cisco products or services, sensitive customer data or employee information, Cisco intellectual property, or supply chain operations,” according to the bulletin. Cisco had delayed announcing the breach pending completion of its investigation into the incident. But when snapshots alleging to contain Cisco data appeared on the dark web on August 8, Cisco responded with the details of their analysis. The sophisticated attack is suspected to have been conducted by an “initial access broker (IAB) with ties to the UNC2447 cybercrime gang, Lapsus$ threat actor group, and Yanluowang ransomware operators,” according to a blog post from Talos, Cisco’s threat intelligence arm.
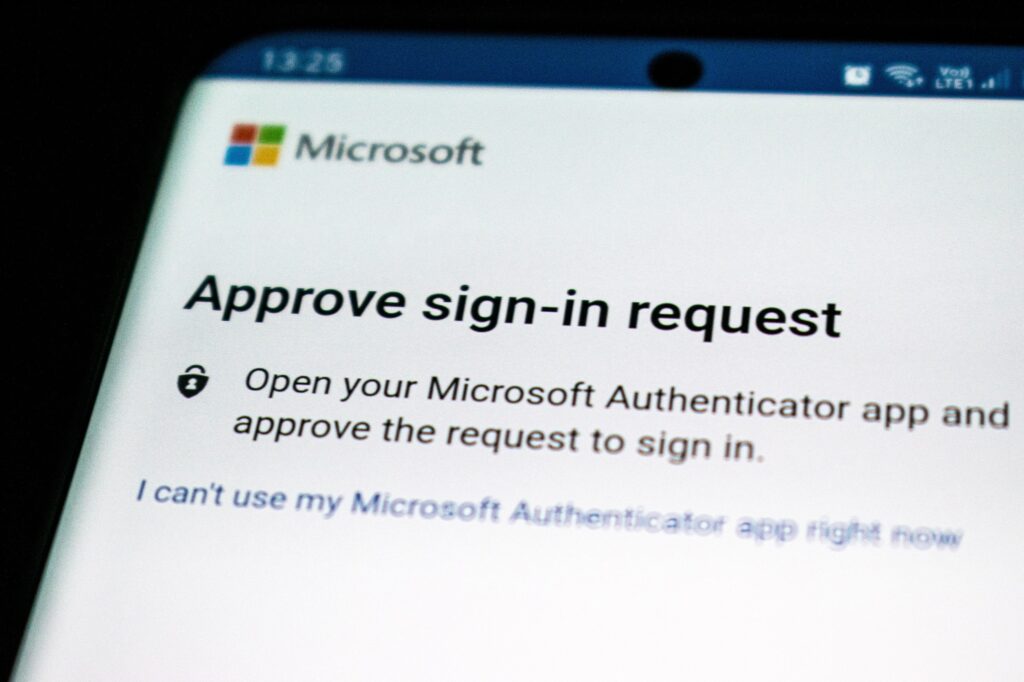
The post explained the initial means of attack, describing “that a Cisco employee’s credentials were compromised after an attacker gained control of a personal Google account where credentials saved in the victim’s browser were being synchronized. The attacker conducted a series of sophisticated voice phishing attacks under the guise of various trusted organizations attempting to convince the victim to accept multi-factor authentication (MFA) push notifications initiated by the attacker. The attacker ultimately succeeded in achieving an MFA push acceptance, granting them access to VPN in the context of the targeted user.”
The Talos blog post provides extensive information on the tactics, techniques, and procedures (TTPs) used by the attacker, and a list of the IOCs observed in the attack. It also outlines Cisco’s response to the incident, which included a company-wide password reset directive, new malware detection signatures, and recommendations for security awareness training, network hardening, backups, and audit.
Motorsport manufacturer BRP reports cyber attack
In a brief news release on August 9, motorsports product manufacturer BRP announced that they had suffered a cyber attack. In an update the next day, company spokesperson Biliana Necheva reported that BRP’s teams “continue working around the clock to resolve the situation and have made progress restoring some [BRP] servers”. No information was provided on the nature of the attack, or if a ransom had been demanded in the incident.
“[W]e are targeting to resume our Valcourt manufacturing operations on Monday, August 15,” continued Necheva, referring to BRP’s flagship factory site. “The rest of our operations remain suspended temporarily, which may delay certain transactions with customers and suppliers.”
Quebec-based multi-national BRP is a prominent player in its sector, with a product line that includes well-known brands Ski-Doo, Sea-Doo, Lynx, Can-Am, and Rotax. The company has billions in annual sales across over 120 countries, and employs nearly 20,000 people across six countries.

Ontario Cannabis Store resumes distribution after supply chain cyber attack
On August 12, the Ontario Cannabis Store (OCS), announced that they are resuming operations and ramping up the fulfillment of retail store orders and deliveries after an August 5 cyber incident disrupted their supply chain.
OCS is the Crown corporation that sells cannabis products online and distributes products to stores across Ontario. They use Brampton, Ontario company Domain Logistics for distribution. Domain Logistics’ parent company – Indiana-based Legacy Supply Chain (LCS) – was hit by a cyber attack on August 5. As a precaution, OCS shut down its systems and was forced to close its warehouse on August 8.
OCS restarted its systems after a “thorough forensic investigation by Domain Logistics’ and OCS’ third-party cyber-security experts [had] determined that no OCS distribution centre systems or customer data was compromised by the incident.” Deliveries are expected to be caught up over the next few days, though as of August 15, the OCS website still warned: “The Ontario Cannabis Store is currently unable to fulfill or deliver orders. Customers placing orders on OCS.ca should expect significant delivery delays.”
Meanwhile, LCS continues its recovery efforts after the cyber incident. In their initial August 5 statement (since removed), they announced that they had “detected unusual activity on our network and immediately implemented our protection protocol. This included taking our network and a number of applications offline and engaging external experts to investigate and remedy the situation”. This affected order processing for a number of customers, including Domain Logistics and OCS.
In their August 12 statement, LCS advised that their “internal network is back online and secure and we are in the process of bringing other servers, networks and customer services back online. We are nearing the completion of the recovery and barring the unforeseen, expect to have fully completed these efforts within the next few days.”
While no details on the nature of the attack were provided, LCS sought to reassure customers by advising that they do not have access to end customer personal financial information, and there is no current indication of a data breach involving “personal or commercially sensitive data”.


